Syslog is a universal log format supported by network devices and Linux applications. Windows applications can also send log data in the syslog format using tools like Windows Snare and nxLog. Many network devices like routers, load balancers and intrusion detection system export logs using the syslog protocol. Syslog can be set up to use UDP or TCP. Sending data over UDP is not reliable, for this reason Logscape Cloud accepts data via TCP only.
1) Configure RsyslogYou will need a syslog daemon to collect log data from your various devices and applications. The instructions below show you how to set up rsyslog to forward log data into Logscape.
Edit your rsyslog.conf using your favourite editor
sudo nano /etc/rsyslog.conf
The LOGSCAPETOKEN refers to your security token which you received on signup and the LOGSCAPETAG is an identifier for the log data.
$template Cloud,"LOGSCAPETOKEN:70657eb1:14999ee959f:-7fd6 LOGSCAPETAG:syslog %timestamp:::date-rfc3339% [%syslogfacility-text%] [%syslogseverity-text%] [%HOSTNAME%] [%app-name%] [%procid%] [%msgid%] %msg%"
*.* @@collector.logscape.com:1468;Cloud
It is possible to send your logs into Logscape Cloud following the RFC 5242 format defined here.
$template Cloud,"LOGSCAPETOKEN:YOUR_TOKEN LOGSCAPETAG:syslog <%pri%>%protocol-version% %timestamp:::date-rfc3339% %HOSTNAME% %app-name% %procid% %msgid% %msg%"
Paste the snippet into your rsyslog.conf and replace only the SECURITY_TOKEN from your account.
2) Restart the daemonRestart your rsyslog daemon.
sudo service rsyslog restart3) Send a test message
You can test your configuration is correct by sending a test message using the logger command
logger THIS IS A TEST MESSAGE
This message will appear in your Logscape account.
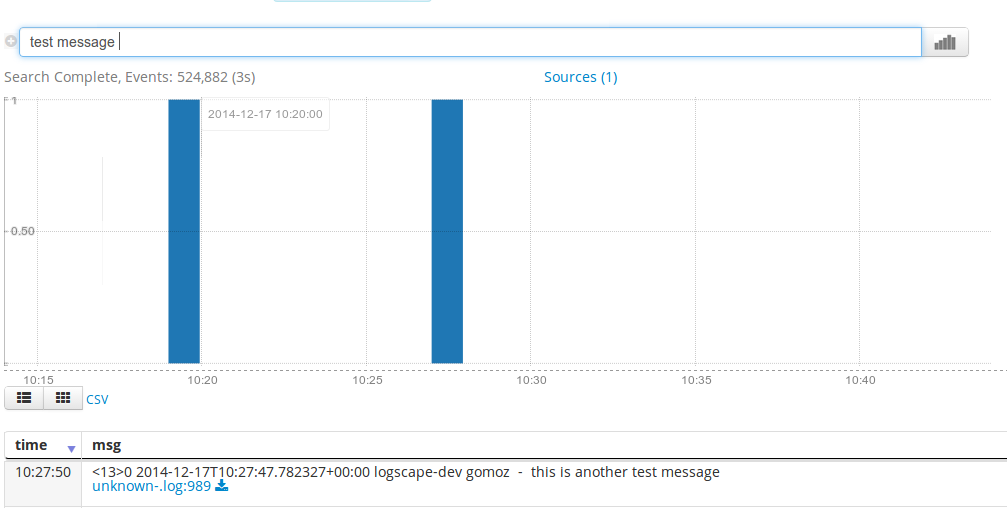
4) Search your syslog data from logscape.Log into your account at cloud.logscape.com and type 'test message' into the search bar, and search the last hour. Your test message will appear in the table below the chart.