These settings define the trigger conditions for an alert. When the trigger condition is met, the alert is fired and any configured alert actions are executed.
Numeric Trigger ConditionThis is the minimum number of events required to trigger the alert. In the example below, if the search returns 3 events or more then the alert is triggered.
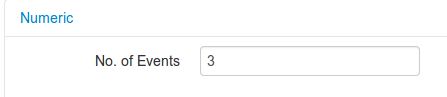
In this example, the alert will fire when 3 valid events are discovered by the trigger search.
ExpressionA search expression can be used as a trigger condition for the alert. Any of the fields available from the search that evaluate to true or false can be entered in this field. The example below shows a cpu based search.
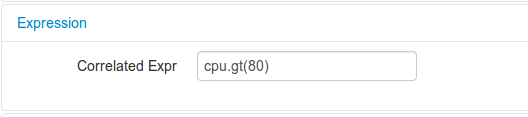
The alert will trigger when the cpu field value is greater than 80%.
CorrelatationCorrelated events are used to study a time window for a sequence of values, or average. While correlated events can be used on almost any form of data, they’re at their best when dealing with data such as audit or webserver logs due to the nature of key value pair error codes, but they will excel in any environment that makes use of error messages or codes.
Correlation events have the following fields
Time Window - The window in seconds to look for your event value
Type - Sequence or Average
Event Value - The sequence(comma seperated or average value to look for)
Correlation Field - The field to check
Correlation Key - Additional field, Allows you to group values, i.e _host, would mean all values would need to be from one host
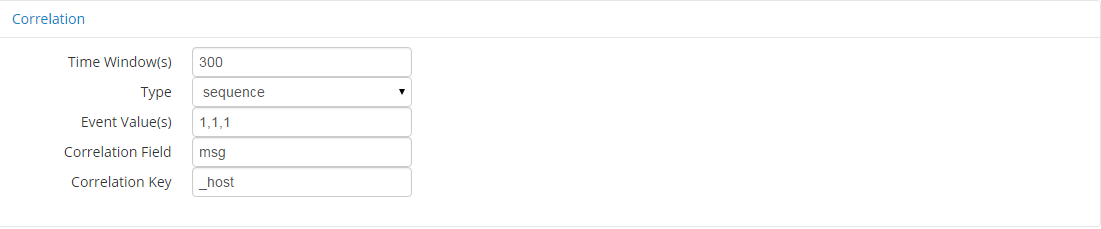
Specifying your type as sequence means that the event must occur N times in a row, without another event inbetween, using the correlation field it is possible to group the events, by for example host, meaning N events in a row must originate from the same host, and events from other hosts will not infringe upon this, When choosing sequence, the values to look for must be added to the event value field and seperated by comma's. Choosing avg will simply average the value over the duration of your capture period.